Documentation Index
Fetch the complete documentation index at: https://docs.safedep.io/llms.txt
Use this file to discover all available pages before exploring further.
Malicious Package Exclusions are available in SafeDep Cloud Pro and above.
See pricing.Only tenant owners can create, edit, or delete exclusions. If you can view package analysis results but cannot manage an exclusion, contact your tenant owner.
Who This Is For
Malicious Package Exclusions are most useful for:- Developers, who experience recurring suspicious package findings and need a clear way to reduce noise
- Tenant owners or security engineers, who decide whether a package should be trusted for their tenant
Where Exclusions Are Respected
Exclusions are designed to work as a tenant-level source of truth for malicious package analysis across SafeDep tools and integrations connected to SafeDep Cloud. This currently includes:- SafeDep Cloud package analysis views in
app.safedep.io - GitHub App
vetin cloud modevet-actionin cloud mode
When To Use An Exclusion
Use an exclusion when:- a package repeatedly shows up as suspicious or malicious, but your team has already reviewed it
- you want to reduce recurring noise without disabling malicious package protection entirely
- you want to trust a package for a limited time by setting an expiry date
What An Exclusion Applies To
Each exclusion is scoped to a package ecosystem, name, and version. You can also add a reason and an optional expiry date for temporary exceptions. Malicious Package Exclusions apply only to malicious package analysis. They do not change vulnerability findings or other SafeDep checks.Create An Exclusion From Settings
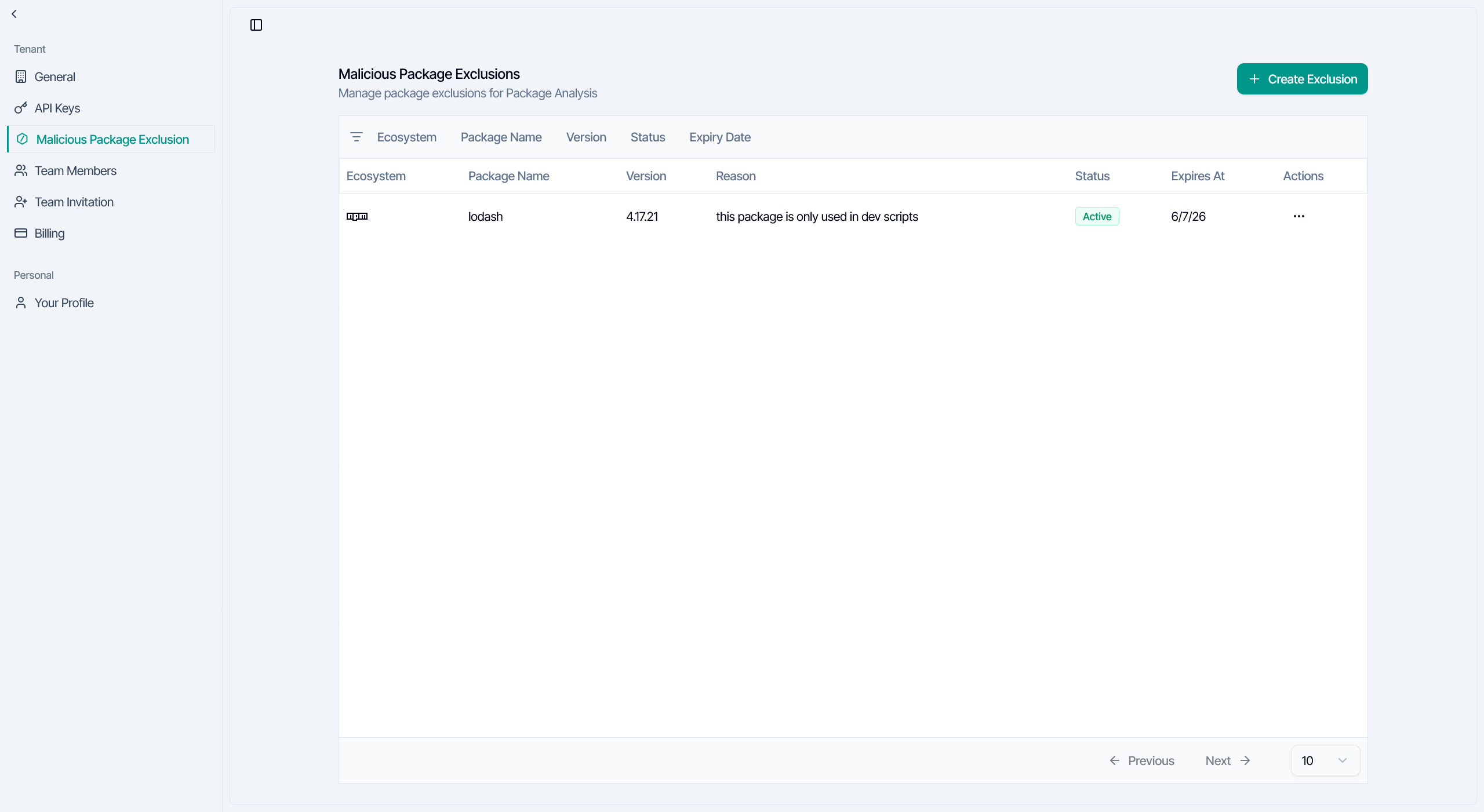
The main place to manage exclusions is the SafeDep Cloud settings page:Navigate to Settings
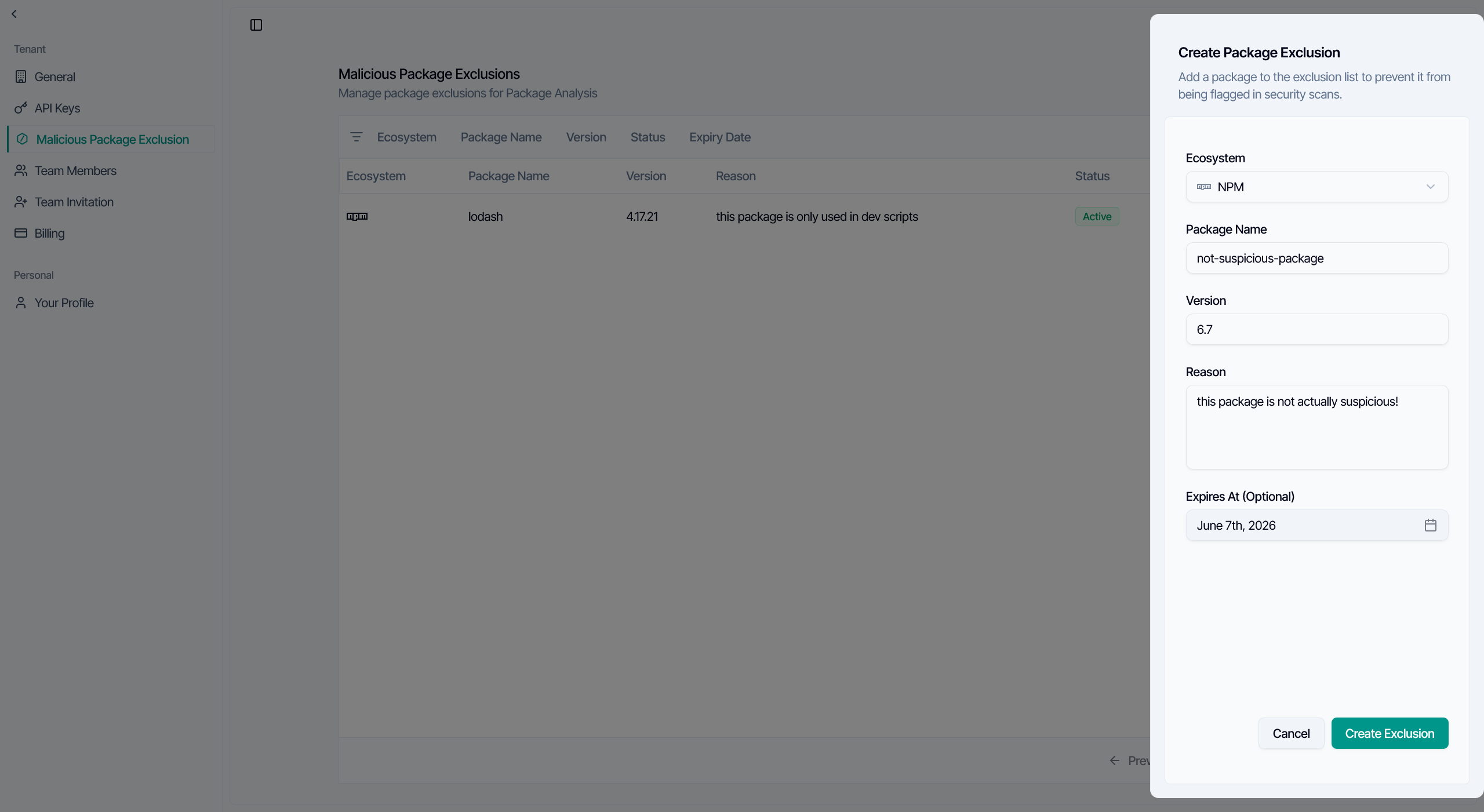
Fields
When creating an exclusion, SafeDep Cloud asks for:- Ecosystem: The package ecosystem, such as npm or PyPI
- Package Name: The package to exclude
- Version: The specific version to exclude
- Reason: Why your team is excluding this package
- Expires At: Optional expiry date for temporary exceptions
0 in the Version field to exclude all versions of a package.
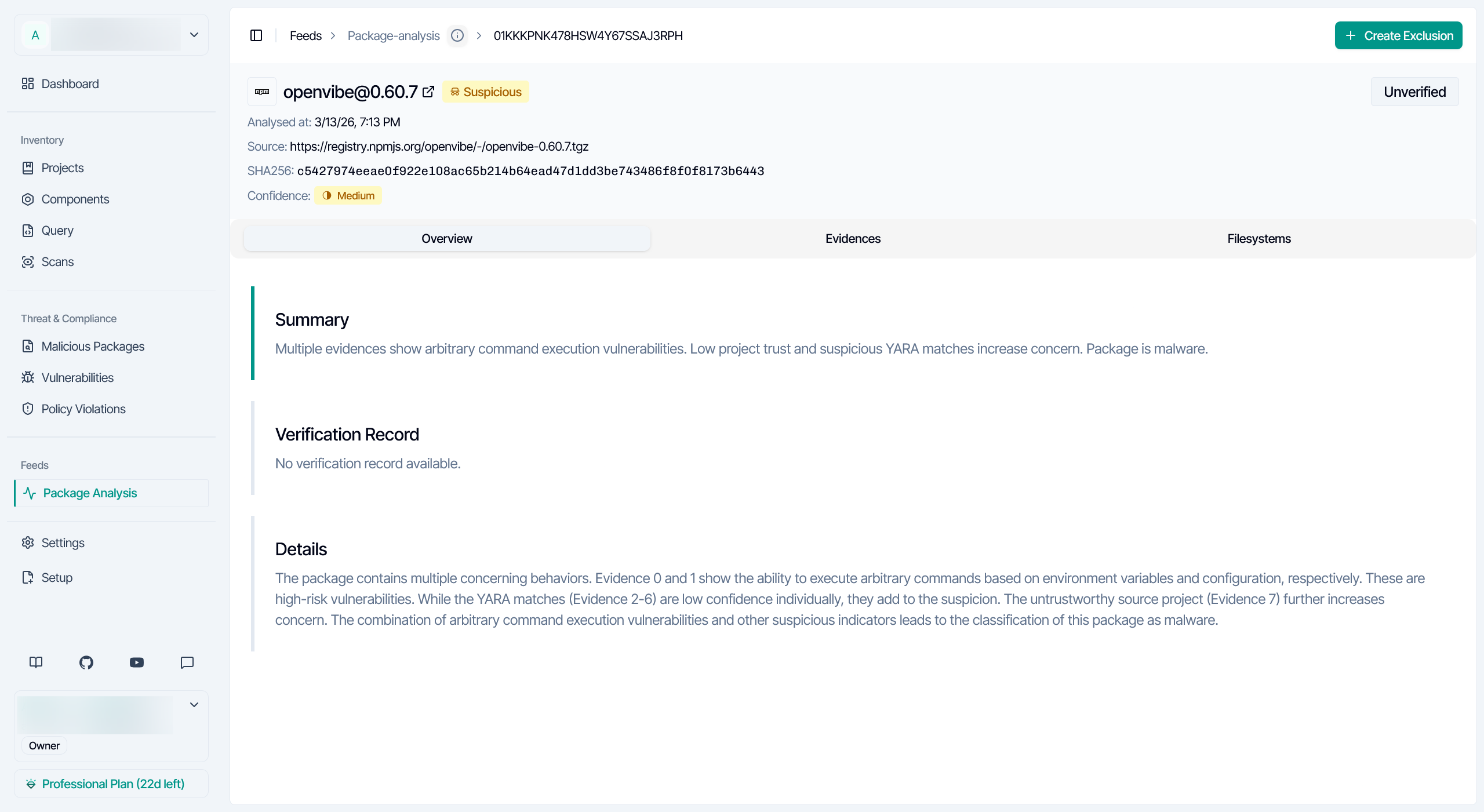
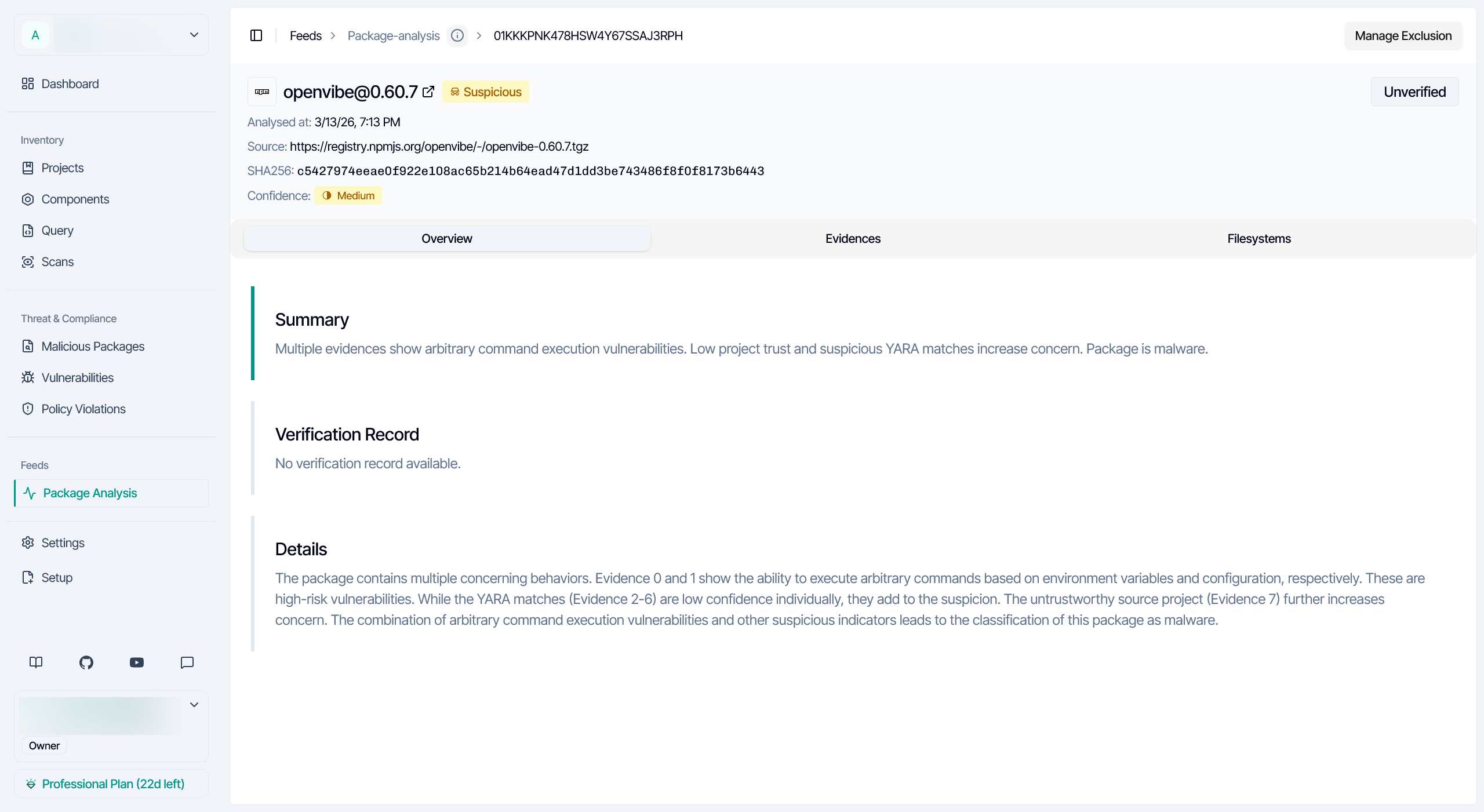
Create Or Manage An Exclusion From Package Analysis
You can also start from a package analysis result:
Depending on the current state, SafeDep Cloud shows one of these actions:
- Create Exclusion if no exclusion exists yet
- Manage Exclusion if an exclusion already exists for that package and version
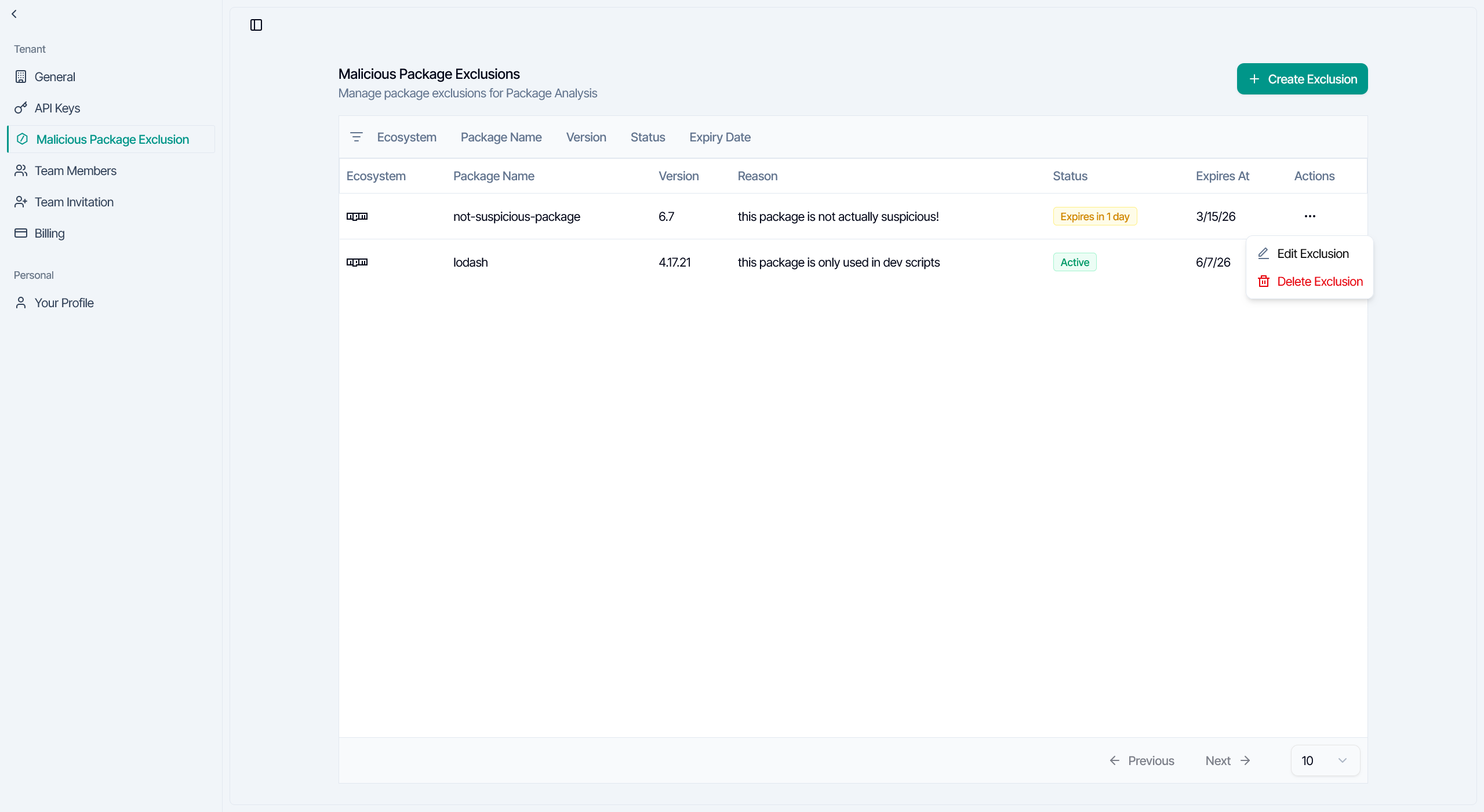
Manage Existing Exclusions
The exclusions table helps you review and maintain the exclusions already configured in your tenant. Each row shows the ecosystem, package name, version, reason, current status, expiry date, and available actions for that exclusion. You can filter exclusions by:- ecosystem
- package name
- version
- expiry status
- expiry date
- edit an exclusion
- delete an exclusion
- review the reason and expiry date attached to each exclusion
- quickly see whether an exclusion is active or close to expiring from the status badge
Edit An Exclusion
Use Edit Exclusion when you need to change:- the version
- the reason
- the expiry date
- the package identity
Delete An Exclusion
Delete an exclusion when you want malicious package analysis to apply normally again. After you delete an exclusion, later scans or package analysis results may surface that package again if it is still detected as suspicious or malicious.How Exclusions Work
SafeDep Cloud applies exclusions using the package identity you provide.Exact Version Vs All Versions
Version is matched exactly.- Enter
4.17.21to exclude only that version - Enter
0to exclude all versions of a package
0 is a special value that means “all versions,” not the literal package version 0.
- If you exclude
lodash@4.17.21, only that version is excluded - If you exclude
lodash@0, all versions oflodashare excluded
Expiry
An exclusion with an expiry date stops applying automatically after the expiry time passes. This makes exclusions useful for temporary investigation windows, migrations, and short-lived exceptions.Verified Malicious Packages
SafeDep Cloud does not allow exclusions for packages that are already verified as malicious. If you try to create or update an exclusion for a verified malicious package, SafeDep Cloud returns an error instead of saving the exclusion. In practice, this means exclusions are meant for packages your team wants to suppress from normal review workflows, not for packages SafeDep has already confirmed as malicious.What To Expect After Adding An Exclusion
After an exclusion is added:- future malicious package analysis for that package should stop surfacing the excluded result across SafeDep tools and integrations that respect tenant exclusions
- the exclusion remains listed on the Malicious Package Exclusions settings page so authorized users can review, update, or delete it later
- depending on the view you are using, you may need to refresh the page or rerun the relevant scan to confirm the updated behavior
Troubleshooting
I can see the page, but I cannot create an exclusion
Exclusion management is currently limited to tenant owners. If the button is disabled, ask your tenant owner to create or manage the exclusion for you.I see a paywall instead of the exclusions table
Malicious Package Exclusions are available in SafeDep Cloud Pro and above. Upgrade your plan or contact your SafeDep representative if you need access.Why did my exclusion stop working?
The most common reasons are:- the exclusion expired
- the package ecosystem, name, or version does not match the current finding
- you may need to refresh the page or rerun the relevant scan to confirm the latest result state
When should I use version 0?
Use version 0 when you want to exclude all versions of a package instead of just one specific version.
Next Steps
GitHub App
See how SafeDep respects exclusions in GitHub pull request checks
Malware Analysis
Learn how SafeDep Cloud analyzes packages for malicious behavior
Authentication
Configure access to your SafeDep Cloud tenant
FAQ
Find answers to common SafeDep Cloud questions

